The increase at the end of the year comes as no surprise. In particular, the return of Emotet is a clear warning signal that cyber criminals will be increasing their attack efforts again in the future. In addition, there are critical security vulnerabilities such as Hafnium or Log4Shell, which act as an invitation for attackers. This is where companies are called on to audit their systems and make them crisis-proof.
G DATA threat report: cyber attacks increase by 25 percent
Cyber defence experts identify a total of more than 23 million different malware samples for 2021
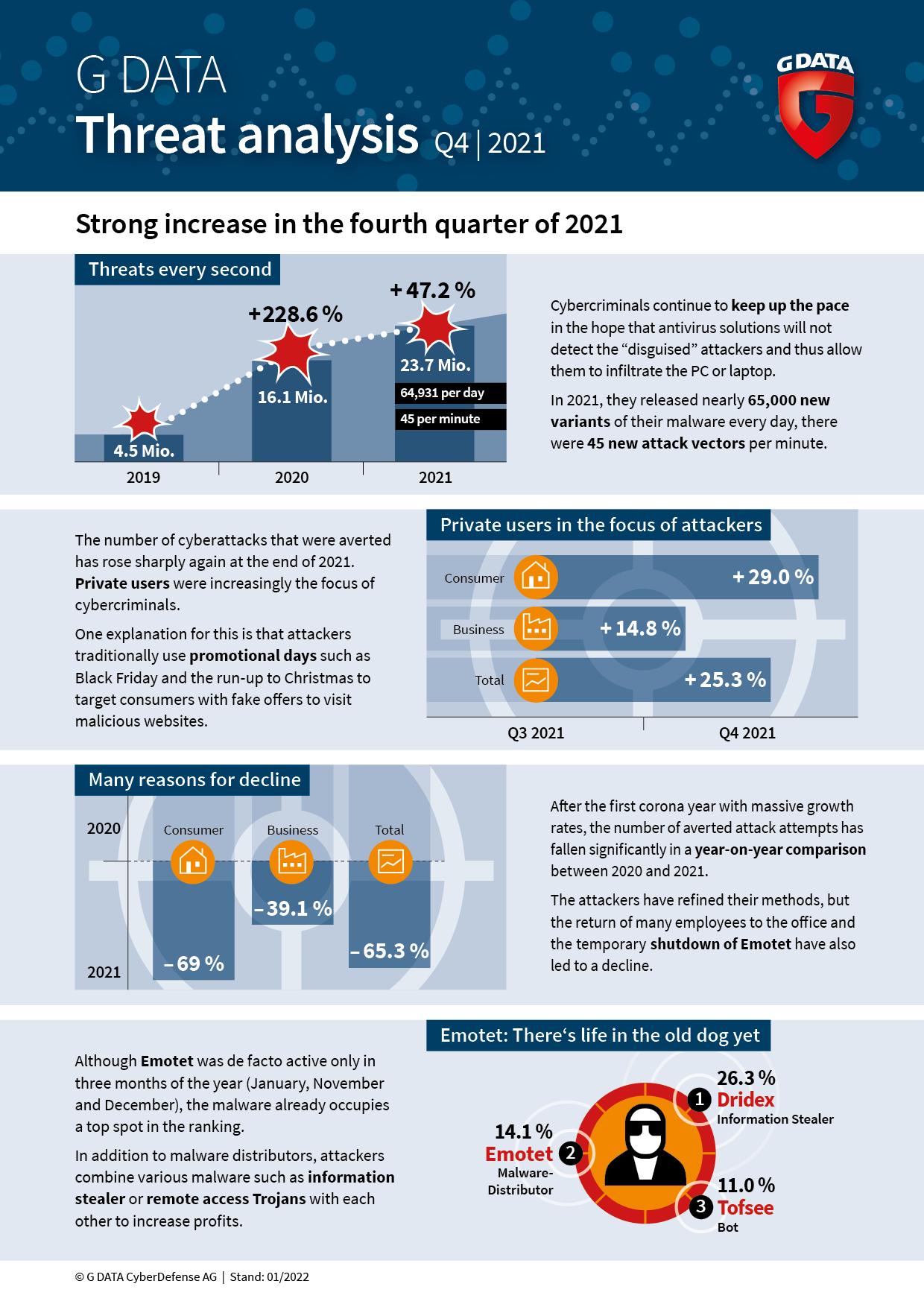
The current G DATA threat report again records a renewed strong increase in averted attack attempts on companies and private users. From the third to the fourth quarter of 2021, the number of attempted attacks increased by 25 percent. The return of Emotet and major security vulnerabilities in internet-facing systems services are just the tip of the iceberg.
The number of averted cyber attacks rose sharply again towards the end of 2021. Cyber defence experts at G DATA recorded an increase of more than 25 percent for the fourth quarter of 2021 compared to the third quarter. Private users were increasingly the focus of cyber criminals here. The number of averted attacks rose by 29 percent, while the increase for business customers was only 15 percent. One explanation for this is that attackers traditionally use promotional days, such as Black Friday and the pre-Christmas period, specifically to invite consumers to visit websites using fake offers.

Emotet: there's life in the old dog yet
After a coordinated takedown in January 2021, Emotet was back again in November 2021. An analysis by G DATA identified more new variants of the malware for the first time. In recent years, Emotet had earned a reputation as one of the most dangerous malwares in existence because it is specifically used as a bridgehead for cyber attacks on companies of all sizes. In the past, an initial infection with the malware was often followed by an attempt to extort money from previously compromised companies through the use of an encryption Trojan. A look at the Malware Top 10 shows how great the danger is. Although Emotet was in fact only active for three months of the year (January, November and December), the malware already holds a top position in the ranking.
Multiple threats every second
However, the following figure shows how great the danger of cyber attacks still is: security experts identified more than 23.7 million different malware samples in 2021. Compared to 2020, this is an increase of over 47 percent, which shows that cyber criminals are continuing to keep up the pace. They have been publishing almost 65,000 new variants of their malware every day - that's 45 new attack vectors per minute - in the hope that antivirus solutions will not detect the “disguised” attackers and will allow them to infiltrate the PC or laptop.
Multiple reasons for the decline in averted attack attempts
Following massive growth rates during the first year of coronavirus, the number of averted attack attempts declined significantly year-on-year. Overall, the cyber defence experts at G DATA recorded 65.3 percent fewer averted cyber attacks in 2021 than in 2020. In the case of private users, attack attempts were reduced by 69 percent, and by 39.1 percent in the case of corporate customers. The reasons for this significant decline are complex. On the one hand, attackers have refined their methods and attacked companies via unsecured remote access or vulnerabilities in public-facing services using attacks such as Log4Shell. But the return of many employees to the office after working from home, as well as the temporary discontinuation of Emotet, have also led to a decline.
Malware Top 10 - old acquaintances and new threats
The Malware Top 10 has changed considerably compared to 2020. On the one hand, there are many new malware families - a total of six of the ten most common malware strains are new. On the other, many different types of malware are represented in this ranking. Until recently, remote access Trojans have always made up a large part of the most frequent types of attack. One explanation for the ranking is that attackers are combining different types of malware with each other to increase profit. For example, they use Emotet as a malware distributor for the initial infection, derive data from the company with an information stealer such as Dridex, and then encrypt the systems with ransomware such as Shade.
The Malware Top 10 at a glance:
| Position | Name | Proportion in percent | Type |
1 (9) | Dridex | 26.3 | Information Stealer | |
2 (1) | Emotet | 14.1 | Malware Distributor | |
3 (-) | Tofsee | 11.0 | Bot | |
4 (-) | Bodelph | 6.3 | Backdoor | |
5 (6) | Trickbot | 6.0 | Malware Distributor | |
6 (-) | Bladabindi | 5.1 | Remote Access Trojan | |
7 (-) | Shade | 5.1 | Ransomware | |
8 (-) | BlackShades | 5.0 | Remote Access Trojan | |
9 (7) | AgentTesla | 4.6 | Information Stealer | |
10 (-) | Pistolar | 4.3 | Dropper | |
Previous year’s position in brackets
“The return of Emotet and vulnerabilities in systems accessible from the Internet are just two of the myriad challenges companies will have to deal with this year,” says Tim Berghoff. “Managers must face reality and make provisions for an IT emergency - just as they must have contingency plans for a fire. The probability of falling victim to a cyber attack is definitely higher than a fire in the office. And those who prepare for it are also able to act in a worst-case scenario and are back in action again more quickly.”
Media:
Allegati
- G_DATA_Tim_Berghoff_MG_0227_300dpi.jpg (6,76 MB)